Blaster - Writeup
Blaster
Reconnaissance
IP: 10.10.137.210
NMAP
nmap -T4 -A -p- 10.10.137.210 -Pn
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-03-09 09:09 EDT
Nmap scan report for 10.10.137.210
Host is up (0.050s latency).
Not shown: 65533 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
80/tcp open http Microsoft IIS httpd 10.0
| http-methods:
|_ Potentially risky methods: TRACE
|_http-server-header: Microsoft-IIS/10.0
|_http-title: IIS Windows Server
3389/tcp open ms-wbt-server Microsoft Terminal Services
| rdp-ntlm-info:
| Target_Name: RETROWEB
| NetBIOS_Domain_Name: RETROWEB
| NetBIOS_Computer_Name: RETROWEB
| DNS_Domain_Name: RetroWeb
| DNS_Computer_Name: RetroWeb
| Product_Version: 10.0.14393
|_ System_Time: 2025-03-09T13:10:35+00:00
| ssl-cert: Subject: commonName=RetroWeb
| Not valid before: 2025-03-08T13:06:46
|_Not valid after: 2025-09-07T13:06:46
|_ssl-date: 2025-03-09T13:10:40+00:00; -34s from scanner time.
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
OS fingerprint not ideal because: Missing a closed TCP port so results incomplete
No OS matches for host
Network Distance: 2 hops
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
|_clock-skew: mean: -34s, deviation: 0s, median: -34s
TRACEROUTE (using port 3389/tcp)
HOP RTT ADDRESS
1 43.42 ms 10.8.0.1
2 43.56 ms 10.10.137.210
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 132.77 seconds
Nmap scan found 2 open ports 80- http and 3389 - rdp
Website
Site
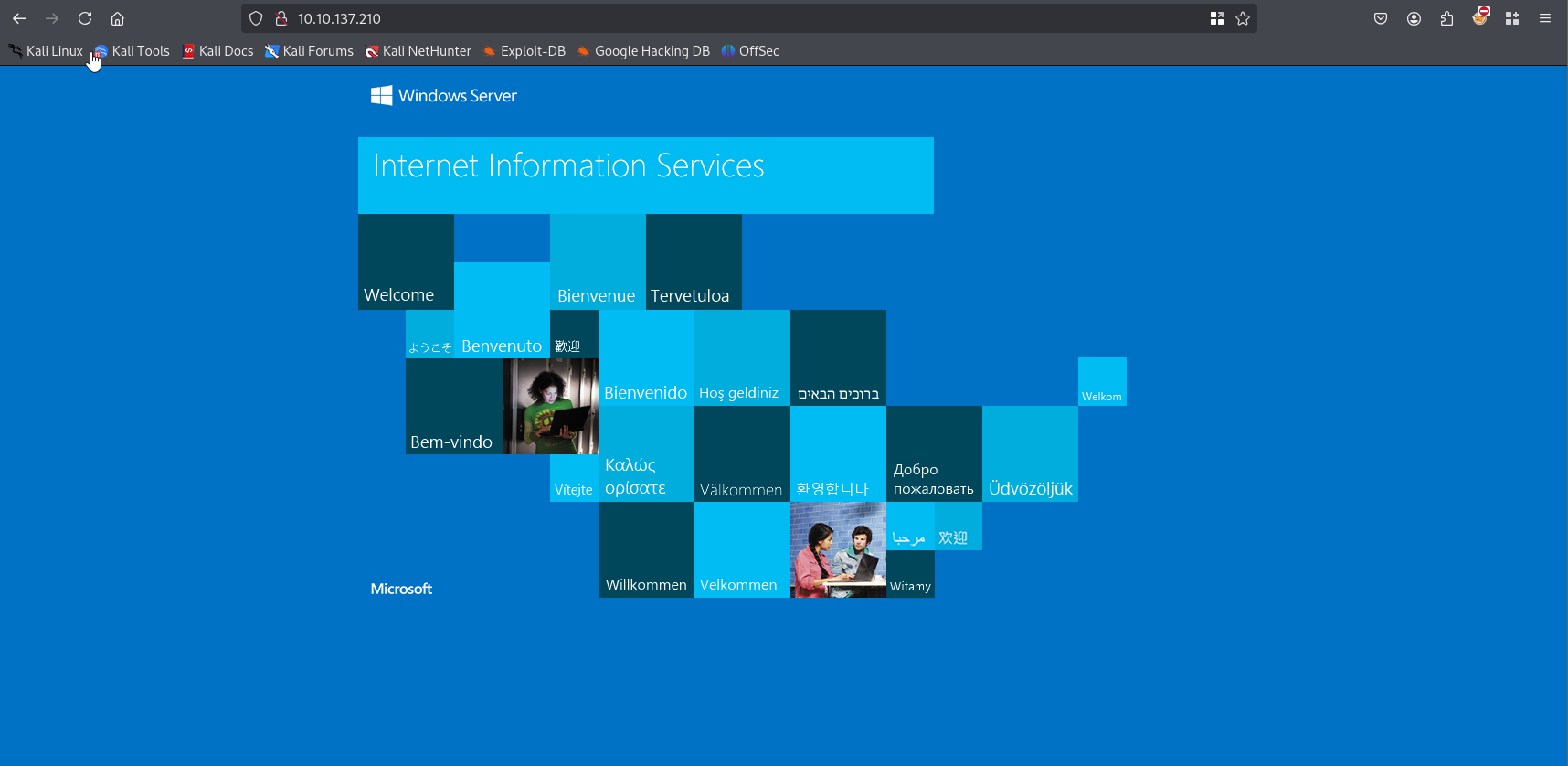
Simple Windows ISS site, let’s search for directories:
ffuf -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt:FUZZ -u http://10.10.137.210/FUZZ
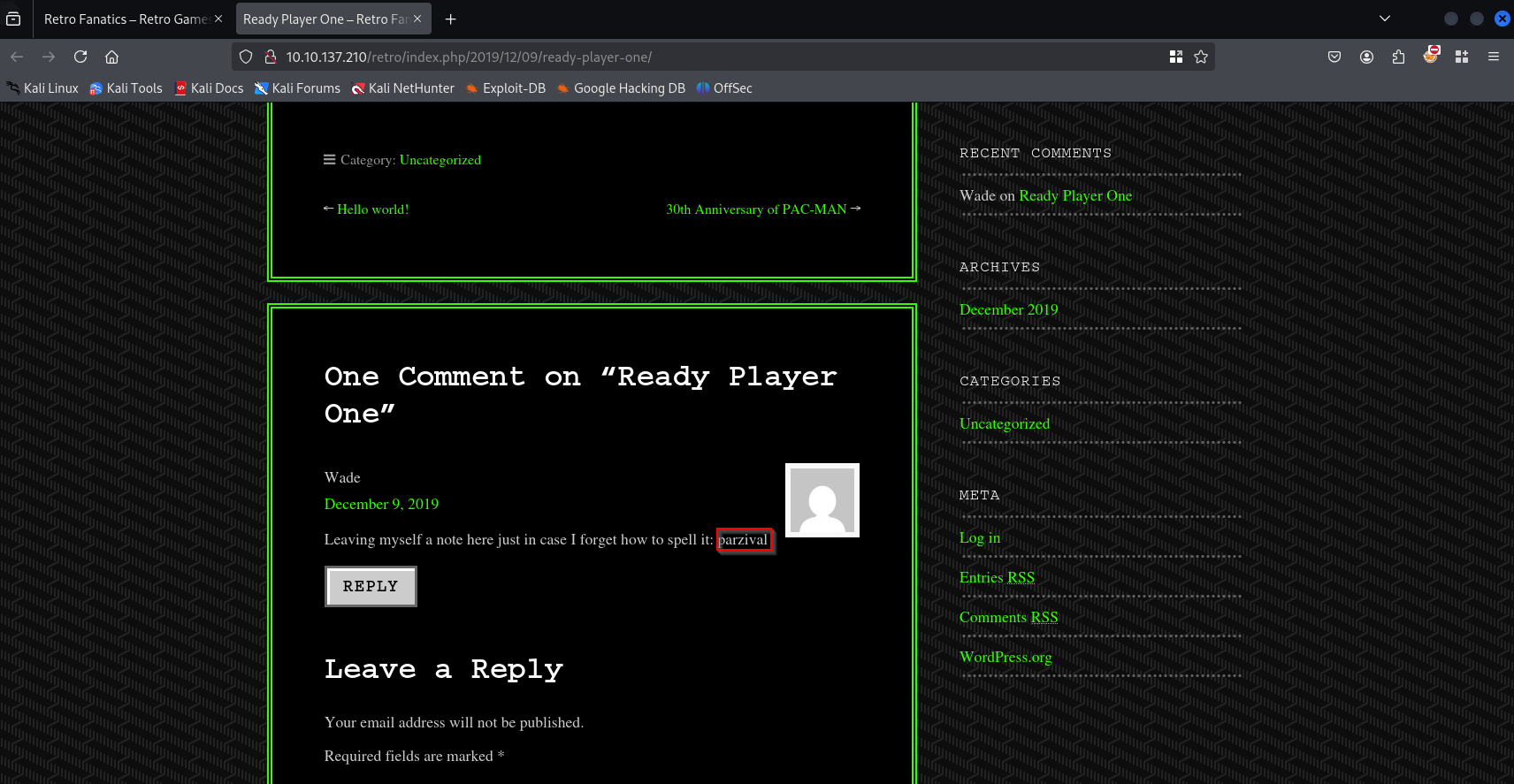
/retro looks like blog. After exploring I we can thing that Wade is admin and I found his password in comment
Gaining Access
RDP
rdesktop 10.10.137.210 -g 95%
Wade
parzival
After log in we see hhupd file, the box is about CVE-2019-1388 so i don’t run winpeas. very simple guide
Privilege Escalation
Find a program that can trigger the UAC prompt screen
hhupd - run as administrator
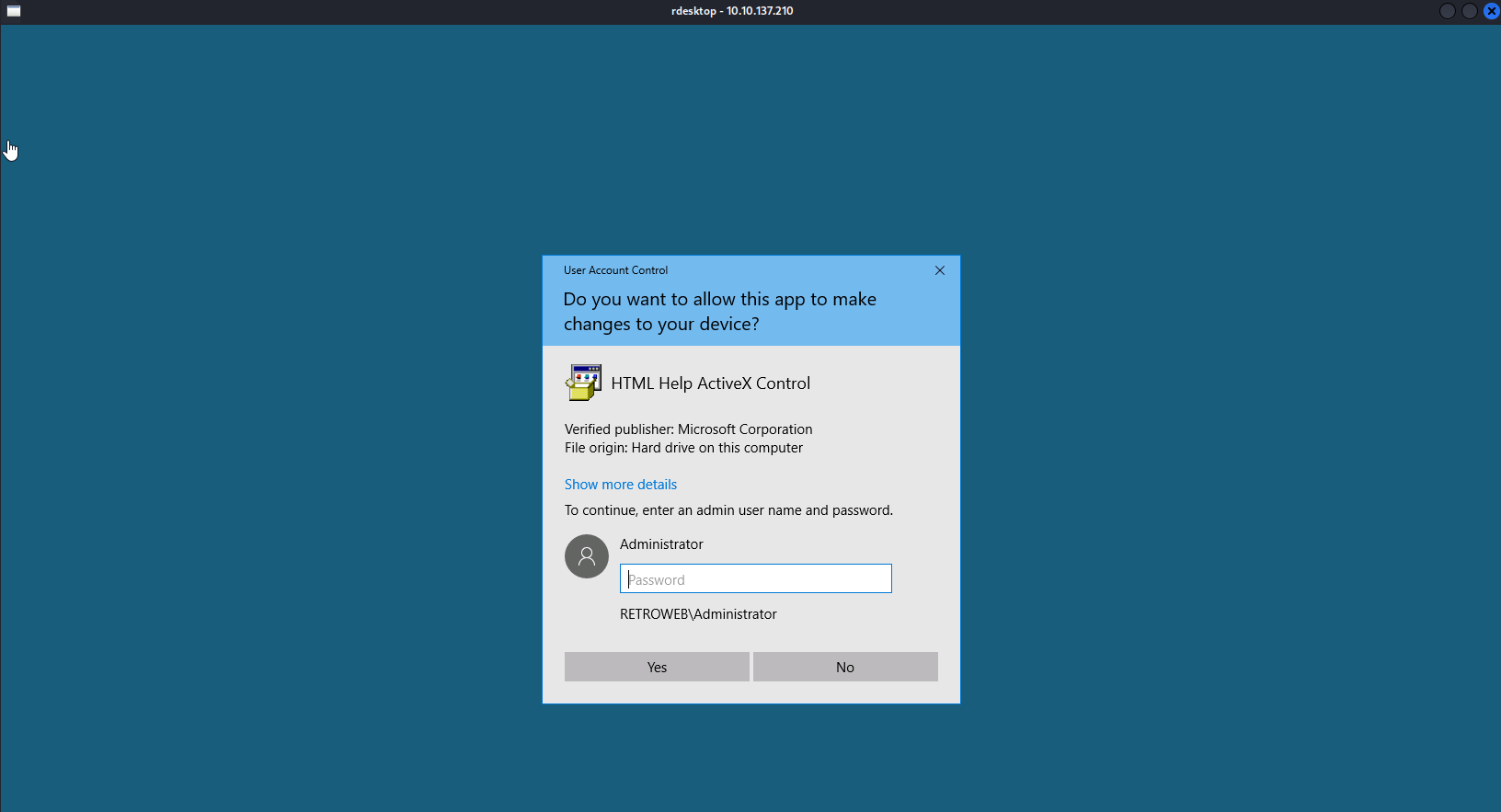
show more details
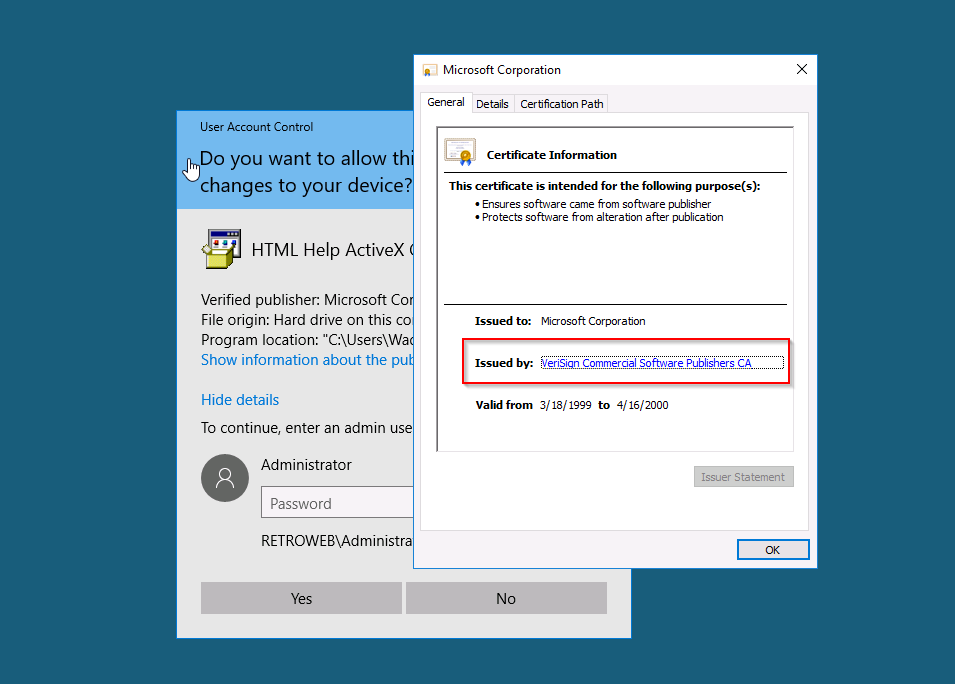
show information about the publisher's certificate
issued by: url(xxxxxxx)
close window
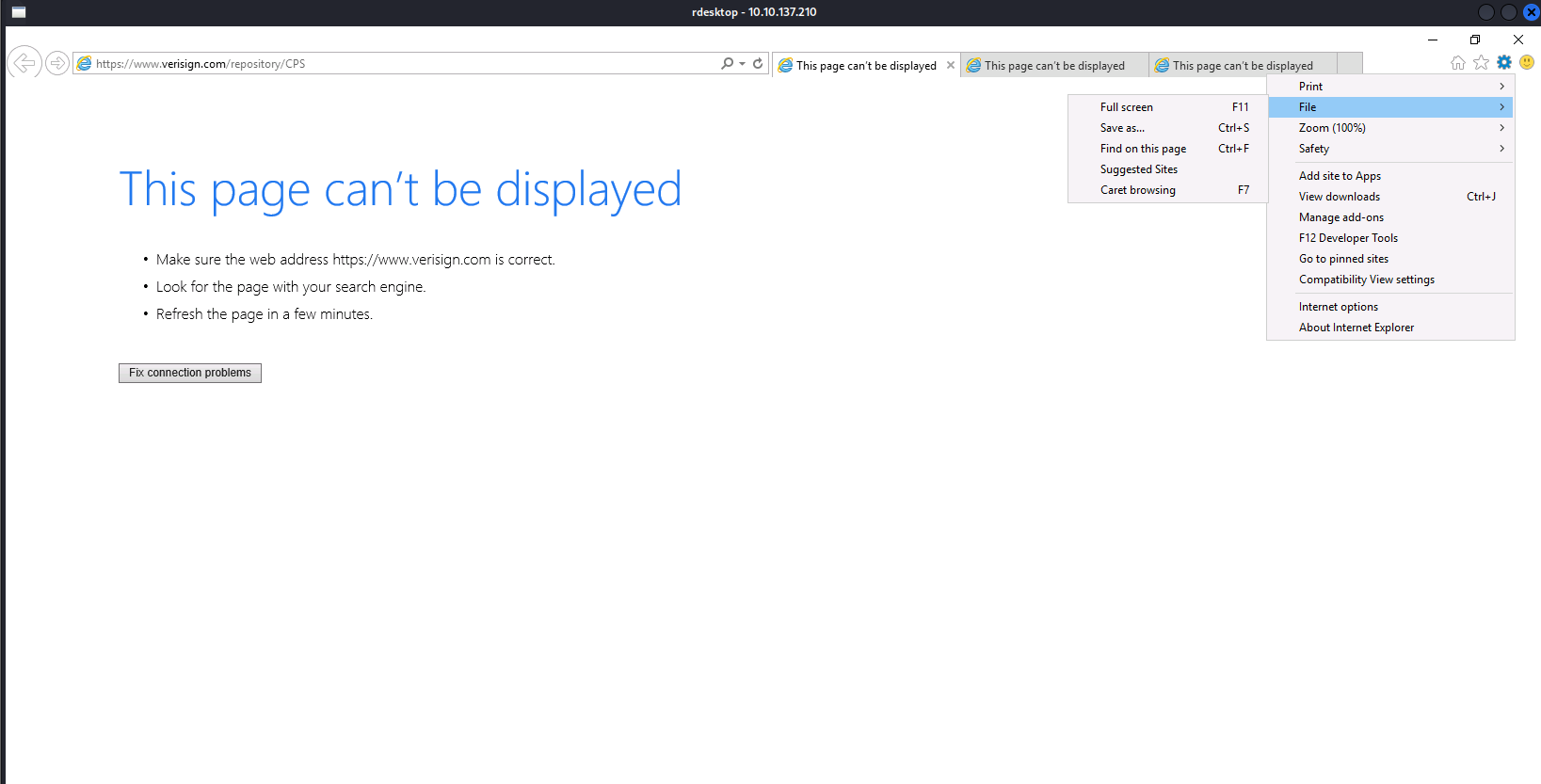
in iexplorer wait for the site to be fully loaded & select “save as” to prompt a explorer window for “save as”.
on the explorer window address path, enter the cmd.exe full path: C:\WINDOWS\system32\cmd.exe
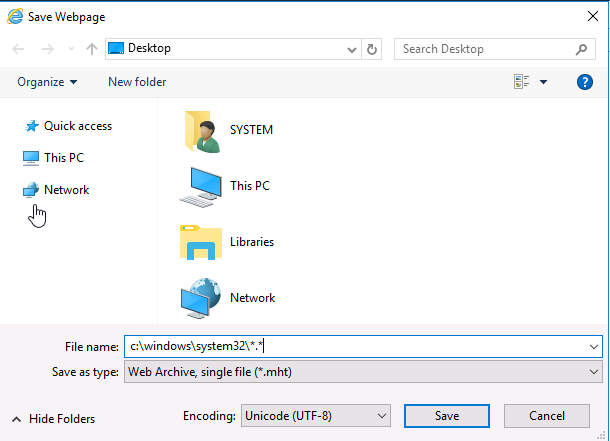
now you’ll have an escalated privileges command prompt.
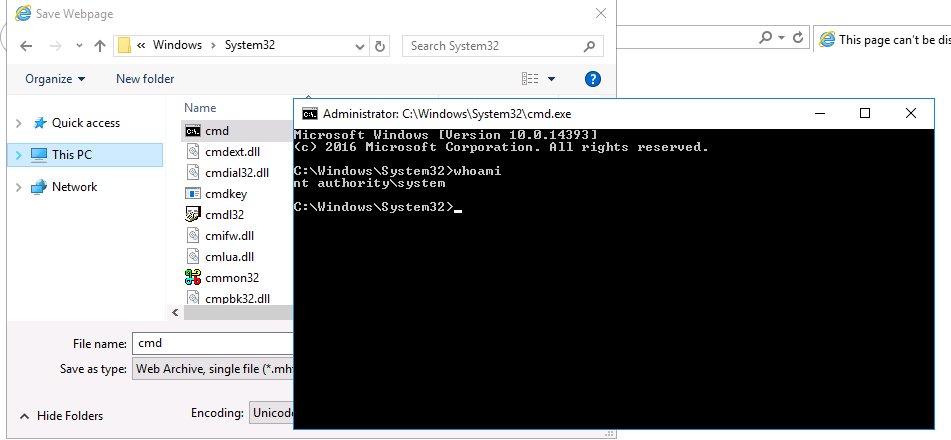
type c:\users\administrator\desktop\root.txt